Home
Quest
Answered
Saved
Hot Topics
Following
Followers
Post
Create
Promote
Comments
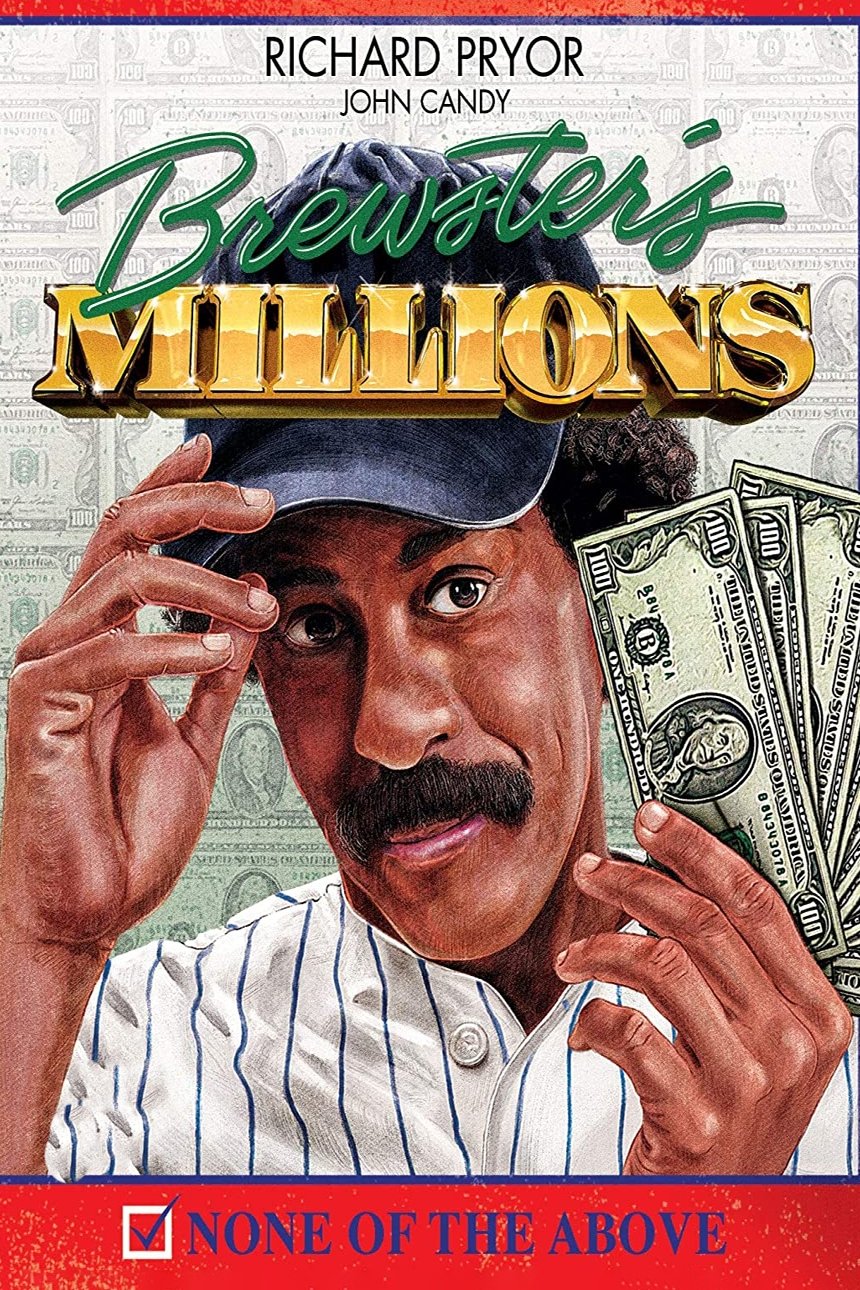
Money
Account